Previous Level: Level 4
Login
SSH: ssh krypton5@krypton.labs.overthewire.org -p 2231
Task
Frequency analysis can break a known key length as well. Lets try one last polyalphabetic cipher, but this time the key length is unknown.
A little bit of Theory
The Kasiski examination is an attack on polyalphabetic cipher that makes it possible to guess the key length. The method looks for repeated sequences and their offsets/distances. The greatest common divisor of the offsets would most likely be the key length.
Solution
This task is similar to the previous one, just that the key length is also unknown. Which means, we have to guess it.
- Just Brute-Force/guess it. Start with key length = 2 and see if the Vigenère Cipher breaker gets a meaningful (English) solution.
- I wanted to see if there is also another, better method to guess the key. I found the Kasiski examination.
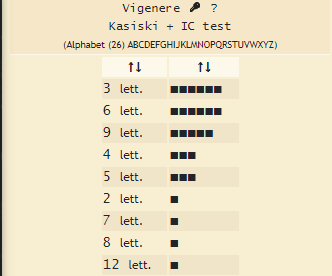
Our trusted Vigenère Cipher breaker from the last task offers this method as well.
The result is that our key is most likely of length 3, 6 or 9. One can see that 6 and 9 are multiples of 3, so the repetition of characters and sequences happened in multiples of 3, given the hint for the key length.
Now that a possible key length has been narrowed down, we can proceed like in the previous level.
This leads us to the correct key length of 9 and the key.
When decrypting the krypton5 file, we get the password for the next level.